We have seen the introduction of numerous devices, catering to different fields, developed by various companies in different parts of the world. This numerous demand and supply of technology called for protocols and standardization. Protocols and standardization assure developers the ability to exchange and use information across different spheres. It ensures that a device made by one company talks to another device made by some other company.
ARCHITECTURE FOR INTERNET OF THINGS [IoT]
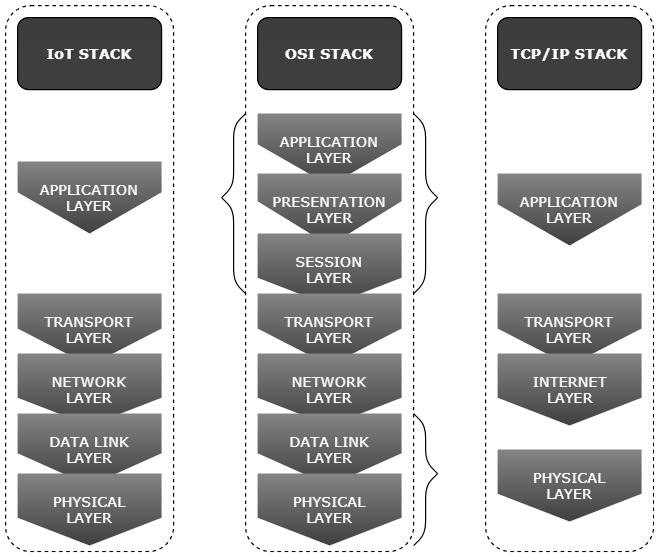
The architecture for the Internet of Things [IoT] has evolved over a period of time. The existing systems of communication over the internet have had its share of influence. Moreover, it was essential to build a system compatible with the existing system and structure. So, in order to understand the existing IoT architectures, let us take a look at its predecessors, the conceptual and existing models of architecture.
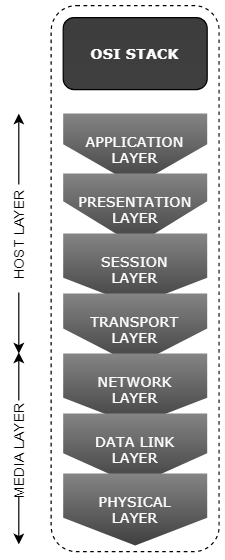
Open System Interconnection (OSI) Model
OSI is a traditional and conceptual model of architecture. It standardizes the communication protocol into abstract layers. It does not take into account the underlying technology. This model is considered as a concept, over which designing of practical models took place.
These are the different layers of the model. The number of the layer is bottom up. Let us take a look at each of the layers, in brief.
- Physical Layer: It defines the physical nature of data transmission. It can be wired or wireless forms of transmission.
- Data Link Layer: It links the data between the two connected nodes between which the communication takes place. It is responsible for detection and correction of errors in the transmission. This layer also takes care of the make and break of the communication. It contains Medium Access Control (MAC) Layer and Logical Link Control (LLC) Layer.
- Network Layer: A network here is a platform of interconnected nodes. Each node has a unique address used to pinpoint each one. This layer provides the means to transfer data (called datagrams) of different length between the nodes.
- Transport Layer: It provides the means to transfer data reliably from a sender to a receiver node. It takes care of the fragmentation and defragmentation of bigger data, enabling retransmission of corrupt data if any. This also takes care of the security in terms of end-to-end encryption.
- Session Layer: It controls the data between the sender and receiver node including the making, managing and breaking the connection.
- Presentation Layer: It acts as a buffer to the application layer and the rest of the transmission process. It converts the data into a form which the application can understand. This is responsible for the compression of the application data.
- Application Layer: It is the layer in which the application developers directly interact with the system. Thus, this is the layer which acts as the buffer between the user (who uses the application) and the process of transmission and reception.
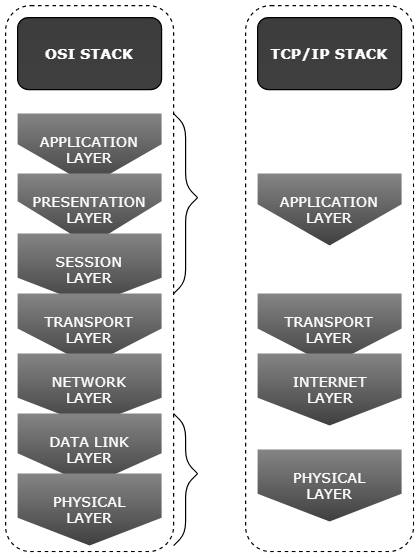
TCP/IP Model
All the layers of the OSI model are not present in the TCP/IP model but most of the functionalities are distributed among the four layers. Thus, the functionality of each layer remains the same as that of OSI model.
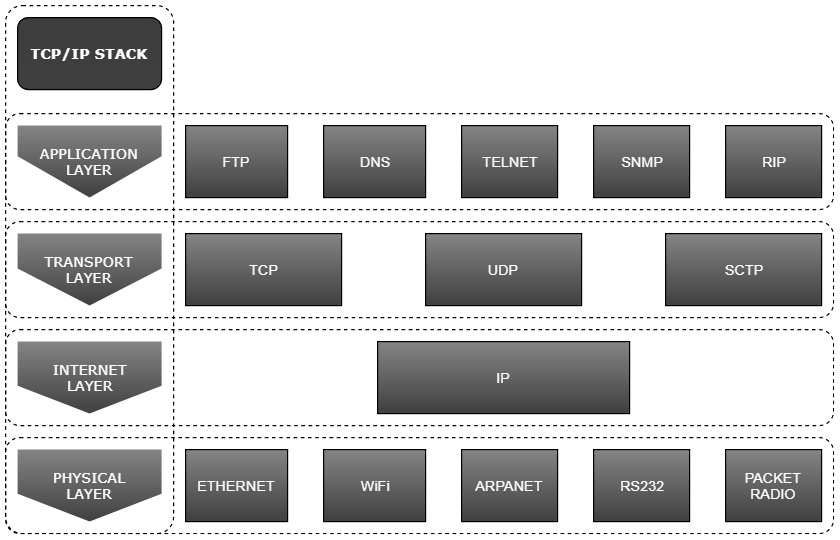
Let us take a look at the protocols that are available in each layer.
Application Layer
- FTP: FTP (File Transfer Protocol) is the commonly used protocol for exchanging files over the Internet. FTP uses the Internet’s TCP/IP protocol to enable data transfer.
- DNS: The DNS Domain Name System) provides a way to match names (a website you’re seeking) to numbers (the address for the website). DNS is like the Internet’s equivalent of a phone book. They maintain a directory of domain names and translate them to Internet Protocol (IP) addresses.
- Telnet: Telnet is a protocol used on the Internet or local area networks to provide a bidirectional interactive text-oriented communication facility using a virtual terminal connection.
- SNMP: SNMP (Simple Network Management Protocol) is an Internet Standard protocol for collecting and organizing information about managed devices on IP networks and for modifying that information to change device behavior.
- RIP: The RIP (Routing Information Protocol) is one of the oldest distance-vector routing protocols which employ the hop count as a routing metric. RIPprevents routing loops by implementing a limit on the number of hops allowed in a path from source to destination.
Transport Layer
- TCP: TCP (Transmission Control Protocol) is a standard that defines how to establish and maintain a network conversation via which application programs can exchange data. TCP works with the Internet Protocol (IP), which defines how computers send packets of data to each other.
- UDP: UDP (User Datagram Protocol) is an alternative communications protocol to Transmission Control Protocol (TCP) used primarily for establishing low-latency and loss tolerating connections between applications on the Internet.
- SCTP: SCTP is a reliable, general-purpose transport layer protocol for use on IP networks. It solved some of the limitations of TCP while borrowing beneficial features of UDP.
Internet Layer
- IP: The Internet Protocol (IP) is the method or protocol by which data is sent from one computer to another on the Internet. Each computer has a unique identifiable address on the Internet which is used to distinguish between each other.
Physical Layer
- Ethernet: Ethernet describes how networked devices can format data for transmission to other network devices on the same network segment, and how to put that data out on the network connection.
- WiFi: WiFi is a wireless technology operating in the 2.4GHz frequency band for local area networking.
- ARPANET: The ARPANET (Advanced Research Projects Agency Network) was an early packet switching network and the first network to implement the protocol suite TCP/IP. Both technologies became the technical foundation of the Internet.
- RS232: RS-232 is a standard communication protocol for linking computer and its peripheral devices to allow serial data exchange.
IoT Model
The functionality of each of the layers remains the same.
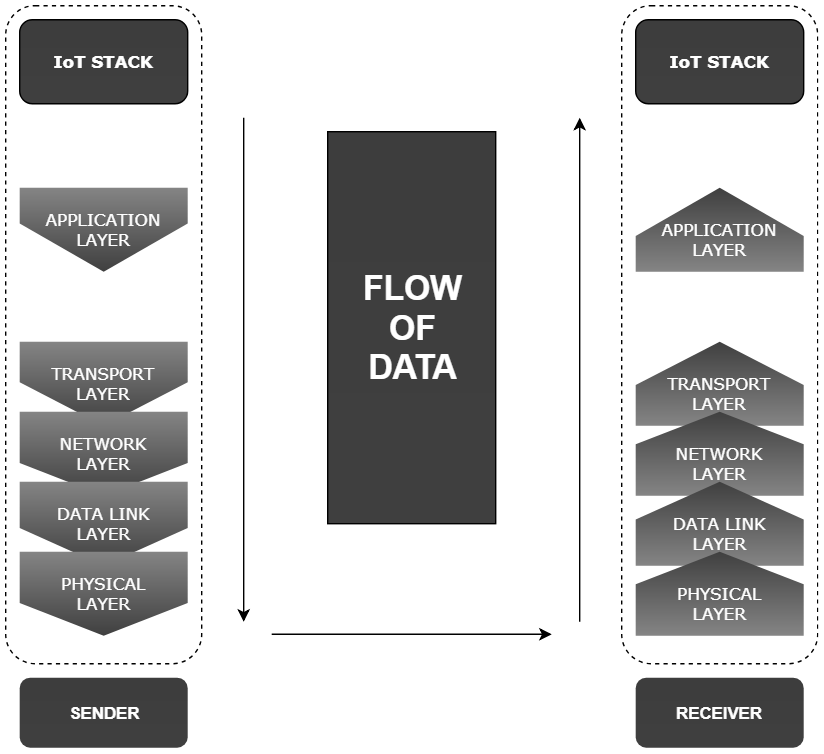
Data Flow
The information flows downward through each layer on the host machine. Each layer in the system adds header and footer to the data to carry out its functions. Application layer generates the data that a user wants to send. Transport layer adds information like squence number, source port, destination port etc. to the application layer. As the next layer, network layer adds its own information over the data coming from transport layer. Network layer adds source and destination IP address. Data Link layer adds Media Access Control (MAC) information. The physical layer too adds data such as the preamble. In some cases, the whole data is rewritten, as in the case of encryption. Thus, each layer adds to the bulk.
Now, at the receiver, the same series of interactions happen, but in reverse order. Each layer sheds the information that the counterpart in the transmitter has added. The shed information is used to carry out each layers’ duty. At the top of the cycle, the application layer extracts and provides the user information.
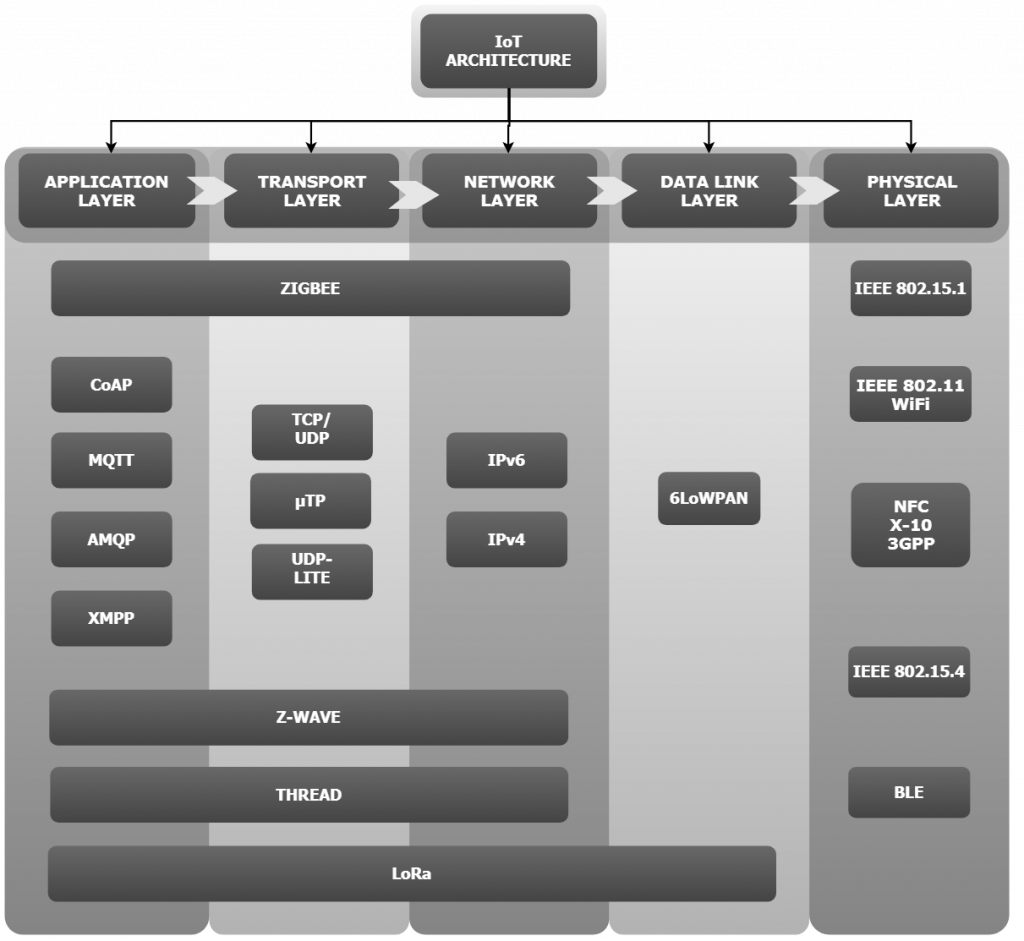
Protocols
Let us take a look at some of the different protocols in each layer.
Let us take a look at each of the layers and protocols.
 CoAP
CoAP
CoAP (Constrained Application Protocol) is a machine-to-machine (M2M), specialized web transfer protocol for use with constrained nodes and constrained networks in the Internet of Things (IoT). The CoAP is not only designed to work with devices on the same constrained network, but also with ones over different networks, offering interoperability. The CoRE (Constrained RESTful Environments Working Group) group has designed CoAP with the following features in mind:
- Overhead and parsing complexity.
- URI and content-type support.
- Support for the discovery of resources provided by known CoAP services.
- Simple subscription for a resource, and resulting push notifications.
- Simple caching based on max-age.
Like HTTP, CoAP is based on the wildly successful REST protocol model: Servers make resources available under a URL, and clients access these resources using methods such as GET, PUT, POST, and DELETE. The link between CoAP and HTTP are also defined. But the difference is that CoAP uses the UDP protocol. This allows proxies to be built providing access to CoAP resources via HTTP in a uniform way. The code footprint for CoAP is very less and thus finds its way into microcontrollers with as low as 10 KB of RAM and 100 KB of code space. CoAP has a good security feature too. CoAP’s default choice of DTLS (Datagram Transport Layer Security) parameters is equivalent to 3072-bit RSA keys.
Advantages
- Will fit in microcontrollers with as low as 10 KB of RAM and 100 KB of code space.
- Follows REST protocol model rendering it easy to implement.
- It has reduced power requirements as it operates over UDP.
- Has smaller packet size, leading to faster communication (even smaller than MQTT).
Disadvantages
- As it uses UDP, the reliability is in question.
- Different standards of CoAP are still evolving.
 MQTT
MQTT
MQTT (Message Queuing Telemetry Transport) is an extremely lightweight connectivity protocol designed to cater to the Internet of Things. It is a machine-to-machine (M2M) protocol which works on publish/subscribe principle of transport of message. The small code footprint for its implementation and open-endedness makes it an ideal candidate for its application in IoT.
There are two types of devices participating in the protocol – brokers and clients. Brokers are the devices which host and relays data. Clients are the devices which access and modify data by publishing topics and receive other devices’ topics by subscribing. Let us take an example of the bulletin board. On the notice board, you might go through the topics which you have interest in. If you have something interesting to put up on the notice board, you are free to do that. To get the attention of the people who are interested in the topic, it is usually done in big bold letters. This is exactly how MQTT works.
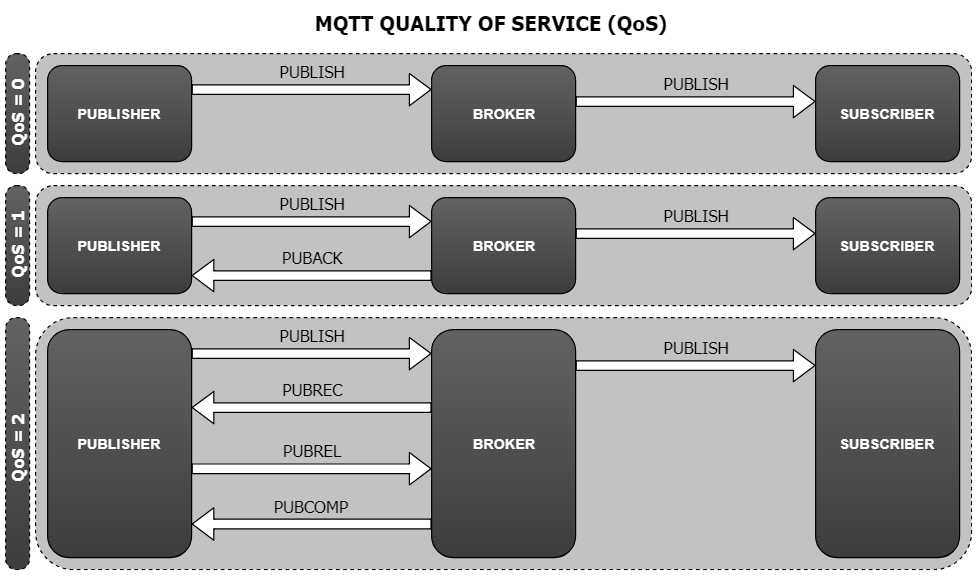
Quality of Service (QoS)
The MQTT also gives a provision for three Quality of Service (QoS) – 0, 1 and 2.
- For QoS = 0, it ensures at most one delivery of the topic. It is equivalent to a ‘fire and forget’ concept.
- For QoS = 1, it ensures at least one delivery of the topic. It receives an acknowledgment. It makes sure that the broker has received the message.
- For QoS = 2, it ensures exactly one delivery of the topic. It gives us an assurance to the delivery of the message.
As the QoS value increases, the time taken for the transmission and reception increases. Thus it will slow down the process of publishing. But, in case of important and critical information, we have to ensure the delivery of the topic, at the expense of time taken. The protocol also has a property called the Last Will and Testament. When the client gets disconnected abruptly from the network, it sends an SOS call. This is used to find the fault with the connectivity.
 XMPP
XMPP
XMPP (Extensible Messaging and Presence Protocol) is a real-time communication protocol for message-oriented middleware based upon open XML (Extensible Markup Language) technology. It was developed for near-time instant messaging (IM), presence information and contact list maintenance. The one thing that makes this protocol unique is that it is an open system since its inception, on 1999. To understand the protocol in a better way let us see what the makers have to say:
- P- Protocol: XMPP is a protocol; a set of standards allowing systems to talk to each other.
- P – Presence: The presence indicator tells the servers that you are online/offline/busy. It, in effect, tells the state of the server.
- M – Messaging: The messaging of XMPP is the part you see. It is the real-time send and received data with a reduced header.
- X – eXtensible: XMPP is an open system and standard, making it extensible.
The developers claim the XMPP to be the most secure messaging standard. “Battle tested. Independent. Privacy-focused.”
The protocol uses a client-server architecture. Every user on the network has a unique JID (Jabber IDs, named after the company who developed the XMPP in the first place). XMPP is a decentralized model – the clients cannot talk to each other and anyone can set-up a server. JIDs are similar to email IDs, with a username and a domain name, separated by at sign, e.g.: [email protected] The name of the resource is at times included in the JID, e.g.: [email protected]/resource. The messages without the resource name get the most priority in all resources for the specific ID. But the messages with the resource name get the most priority in the resources specified in the ID.
Advantages
- Like MQTT, XMPP also makes use of the publish/subscribe mechanism of data sharing.
- It uses the protocol on long-lived Transmission Control Protocol (TCP), ensuring reliable communication.
- It also has secure authentication (SASL) and encryption (TLS) implemented, ensuring security.
- The decentralized approach enables the system to work in isolation, further enhancing the security.
Disadvantages
- But there are some disadvantages. XMPP does not have a Quality of Service (QoS), like that of MQTT.
- Further, the text-based communication increases the overhead when compared to its binary based equivalent.
 AMQP
AMQP
The AMQP (Advanced Message Queuing Protocol) is an open standard, binary, application layer protocol for message-oriented middleware. Originated in 2003 as co-operative open effort, AMQP focuses on passing business messages between applications or organisations. AMQP doesn’t require the systems to be simultaneously available and works reliably over a distance or over poor networks. Like MQTT, AMQP also supports the publish/subscribe protocol of communication. It also has the Quality of Service (QoS) implemented, ensuring the safe passage of important data.
The AMQP specification is defined in several layers:
- a type system,
- a symmetric, asynchronous protocol for the transfer of messages from one process to another,
- a standard, extensible message format and
- a set of standardized but extensible ‘messaging capabilities.’
The basic unit of data in AMQP is a frame. There are nine AMQP frame bodies. These are used to initiate, control and tear down the transfer of messages between two peers. These are:
- open (the connection)
- begin (the session)
- attach (the link)
- transfer
- flow
- disposition
- detach (the link)
- end (the session)
- close (the connection)
Advantages
- Like MQTT, AMQP also makes use of the publish/subscribe mechanism of data sharing.
- AMQP is a wire-level protocol (data send as stream of bytes), ensuring interoperability.
- Simple peer-to-peer and communication with intermediaries possible.
- Protocol has the space to evolve to suit different standards.
Disadvantages
- Backward compatibility with older versions is not supported.
- It is not as simple as HTTP 1.0 or HTTP 1.1 or other wire protocols.
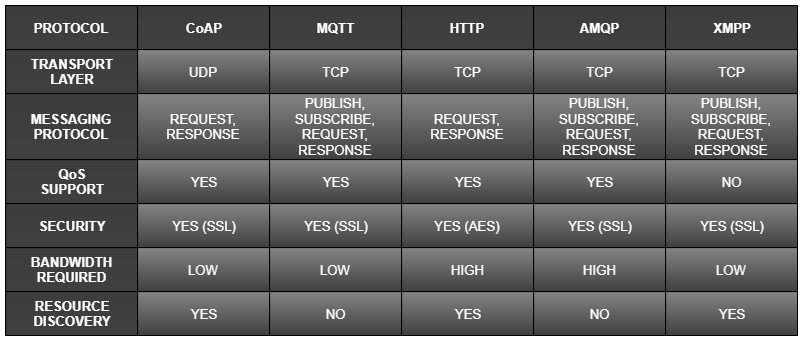
Comparison
 6LoWPAN
6LoWPAN
6LoWPAN (IPv6 over Low-Power Wireless Personal Area Networks) is the name of a concluded working group in the Internet area of the IETF. The main aim of the protocol is to enable the smallest devices to use the internet protocol. This takes into consideration the low-power working condition and the low bandwidth of the devices. And thus, developing a protocol which acts as a bridge between the bigger and smaller devices was very hard.
IETF (Internet Engineering Task Force) is an organization that defines and promotes standards used on the Internet. 6LoWPAN is a group set up within IEFT to standardize a protocol over the data link layer. The 6LoWPAN group uses the IEEE 802.15.4 standard to provide the lower layer elements of this wireless sensor network. The 6LoWPAN group has then defined the encapsulation and header compression mechanisms that enable the IPv6 data to be carried of the wireless network.
IEEE 802.15.1
IEEE 802 standards committee is a committee which specifies wireless personal area network (WPAN) standards. Categorized under IEEE 802 standards committee, IEEE 802.15 is a working group under the Institute of Electrical and Electronics Engineers (IEEE). IEEE is a professional association which standardizes protocols for data communication. Task group one of the IEEE 802 standards committee deals with the 802.15.1: WPAN/Bluetooth technology.
IEEE 802.15.1 defines physical layer (PHY) and Media Access Control (MAC) specification for wireless connectivity. It brings under its umbrella fixed, portable and moving devices within or entering personal operating space. IEEE 802.15.1 standards were issued in 2002 and 2005.
IEEE 802.15.4
IEEE 802.15.4 is a standard developed in 2003 and maintained by the IEEE 802.15 working group. It defines the operation of the physical and media access control (MAC) layer for low-rate wireless devices, which are the typical IoTs. It is the most used IoT standard for MAC. For low powered devices, the frame formats that the traditional networks offer is bulky. This enabled the evolution of IEEE 802.15.4 standard. In 2008, the introduction of IEEE 802.15.4e extended the IEEE 802.15.4 functionality to include the support for low power devices. The introduction of IEEE 802.15.5 defined a mesh networking capability to IEEE 802.15.4.
The operation of IEEE 802.15.4 is in the physical layer, within the unlicensed frequency band. Rest of the layers are undefined and are customized to suit the requirement. The unlicensed frequency bands are:
- 868.0–868.6 MHz: Europe, 1 communication channel.
- 902–928 MHz: North America, up to 30 communication channels.
- 865–867 MHz: India (MTP of 1-4 Watts ERP) with 200 kHz carrier bandwidth.
- 2400–2483.5 MHz: worldwide use, up to 16 communication channels.
 Bluetooth Low Energy (BLE)
Bluetooth Low Energy (BLE)
The Bluetooth low energy is commonly known as BLE or Bluetooth 4.0 and marketed as Bluetooth Smart. Bluetooth Special Interest Group (Bluetooth SIG) designed and marketed this wireless personal area network technology. BLE is an intelligent and low-power version of the classic Bluetooth wireless technology. The use of BLE in today’s products have increased drastically because of some important benefits over the classic Bluetooth technology:
- Lower implementation costs
- Multi-vendor interoperability
- Enhanced range
- Much improved pairing speed
BLE is used in battery-powered devices developed for industries like healthcare, fitness, beacons, security, and home industries. The devices usually transmit a small amount of data as bursts at 1 Mbps speed. However, it is not suitable for sending data in real-time. Some of the features of BLE are:
- Location Detection Accuracy: BLE is used as beacons for micro-locating.
- Proximity Detection: The proximity data provided by BLE is much more accurate than Wi-Fi, but not very accurate either.
- Power Consumption: BLE is a low-power lo-latency technology.
What is the target market of BLE? Let’s take a look:
- low-power requirements, usually for months or years on a button cell,
- small form factor,
- low cost,
- faster and secure connection,
- compatibility with a large installed base of mobile phones, tablets and computers.
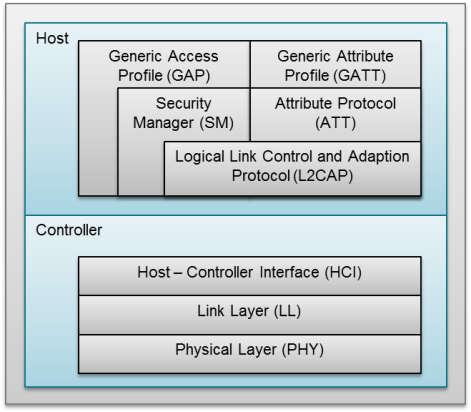
Bluetooth Low Energy Protocol Stack
Bluetooth Low Energy Protocol Stack (Source)
The Host
- Generic Access Profile (GAP),
- Generic Attribute Profile (GATT),
- Logical Link Control and Adaptation Protocol (L2CAP),
- Attribute Protocol (ATT),
- Security Manager (SM),
- Host Controller Interface (HCI), Host side.
The Controller
- Host Controller Interface (HCI), Controller side
- Link Layer (LL)
- Physical Layer (PHY)
 X-10
X-10
X-10 is a protocol for communication among IoT devices, mainly in the home automation sector. It is called as the father of modern home automation. The existing household wiring, which powers the house, acts as the physical layer to transmit and receive data. Signaling and control of devices use small bursts of radio frequency representing digital information. The digital data is modulated using a 120KHz frequency which is superimposed on the relatively quiet, zero crossings of the AC supply. These digital signals can transport any information, from binary values to float values, depending upon the use case. X-10 devices are connected to the plugs in the wall, like a normal electrical appliance.
Protocol
The x-10 packets consist of ‘house code’ followed by one or more than one ‘unit codes’ and terminated by a ‘command code’. Each of these is four bit long. The house code is a letter from A to P while a unit code is a number from 1 to 16. One house code, along with one unit code, addresses each device. Each device in the X-10 network responds to a unique address assigned to it. Thus, an X-10 network can have 256 possible addresses (16 house codes × 16 unit codes).
Introduction of an RF protocol made it possible to interface the wireless devices such as wireless keypads, motion sensors and remote switches. This uses an NEC IR for transmission and a bridge to connect the two technology protocols.
Advantages
- The infrastructure for the medium of communication exists and thus needs less effort to set-up.
Disadvantages
- The data rate of signal transmission is very less, in the order of 20 bits/s. Thus, this technology facilitates for turning on and off devices only.
- We cannot increase the rate of transmission as the transformer will drop high-frequency signals.
- The electrical system of a house needs to block the X-10 signals from going out as it can interfere with the signaling and control of the neighborhood.
- Interference in the power cables hinders the transmission of X-10 instructions.
- Although this was a useful technology, more reliable and secure technology and protocols is slowly replacing X-10. As a result, this technology and protocol are considered obsolete.
 Zigbee
Zigbee
Zigbee is a low powered, low cost, standard on a wireless mesh network designed for battery-powered devices. It follows IEEE 802.15.4 protocol for its personal area networking. Zigbee is designed for home automation, energy meters and other Internet of Things (IoT) device applications. Thus, it sports a small, low power digital radio with low bandwidth consumption, ideal for such applications.
Zigbee was developed in 1998 and standardized in 2003. WiFi and Bluetooth are the wireless personal area networks that Zigbee aimed to substitute. Compared to WiFi and Bluetooth, Zigbee is able to transmit data over a longer distance (10-100m line of sight) with lower latency. Supporting low power devices too increases the mileage of Zigbee over its competitors.
Zigbee Architecture
The Zigbee system has three different types of devices:
- Zigbee Coordinator: There should be at least one coordinator in each of the systems. It acts as a root and bridge to the network. While transmitting and receiving information, it is responsible for the handling and storing of messages.
- Zigbee Router: Like a WiFi router, the Zigbee router acts as an agent in passing the information from one device to another.
- Zigbee End Device: The battery-powered units of the Zigbee architecture are called the end devices. It senses, collects and reports data. The communication with the coordinator via the router is very short in order to save power.
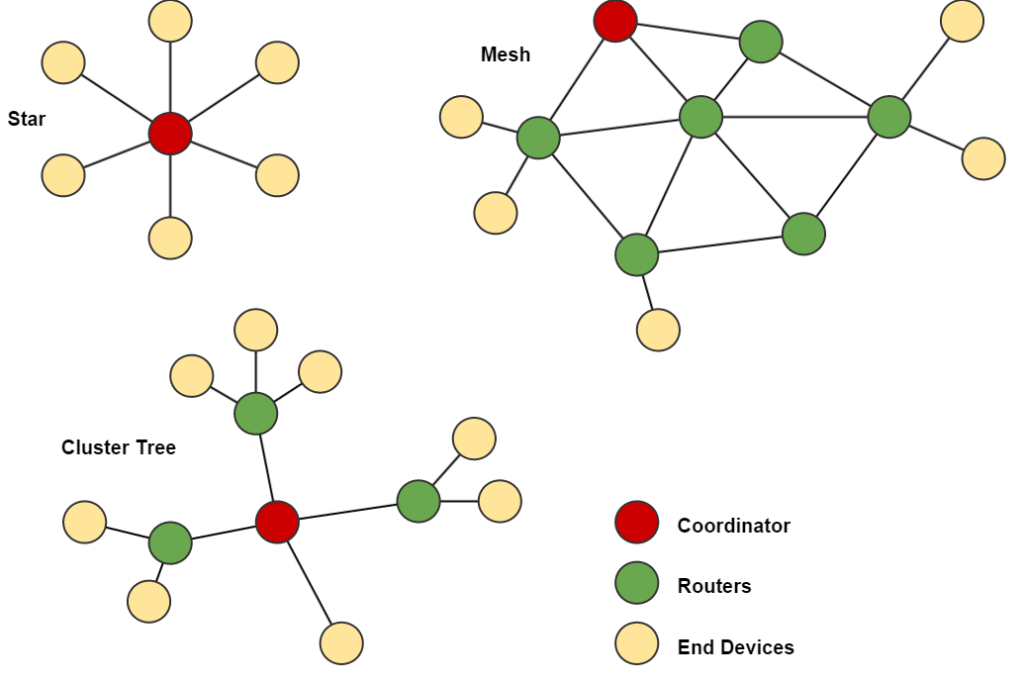
Zigbee Topologies
The number of Zigbee coordinators, Zigbee routers and Zigbee end devices depend upon the topology used. The most common topologies Zigbee supports are:
Star, mesh and cluster tree topologies with coordinator, routers and end devices (Source)
- Star topology: It consists of one coordinator. All the end devices connect to this coordinator. Thus it has the sole responsibility to manage all the end devices.
- Mesh topology: It consists of interconnected routers, bridging the communication with the lone coordinator and the end devices.
- Cluster tree topology: It consists of routers with end devices as leaves, connected to a coordinator.
Zigbee Protocol
Zigbee Protocol Stack
- Physical Layer: This layer does modulation and demodulation operations upon transmitting and receiving signals respectively.
- MAC Layer: This layer is responsible for reliable transmission of data by accessing different networks with the carrier sense multiple access collision avoidance (CSMA). This also transmits the beacon frames for synchronizing communication.
- Network Layer: This layer takes care of all network related operations such as network setup, end device connection and disconnection to network, routing, device configurations, etc.
- Application Support Layer: This layer enables the services necessary for Zigbee device object and application objects to interface with the network layers for data managing services. This layer is responsible for matching two devices according to their services and needs.
The ZigBee protocol uses the 802.15.4 standard and operates in the 2.4 GHz frequency range with 250 kbps speed. The maximum number of nodes in the network is 65,560 (ZigBee PRO) with a range up to 100 metres. ZigBee can use 128 bit AES encryption.
 Z-Wave
Z-Wave
Z-Wave, developed by Zensys, is a mesh network wireless protocol. It uses low-energy, unlicensed frequency band in the 800-900 MHz range. It allows wireless control of home appliances and other devices, making it apt for home automation. The system has a central control device which acts as both the hub controller and the portal to the outside communication. This device lets the user control the appliances through wireless key fobs, a wall-mounted keypad or through smartphones, tablets or computers.
Z-Wave technology has seen a good market. From six products in 2005, the protocol has powered 2400 interoperable devices, as of mid-April, 2018.
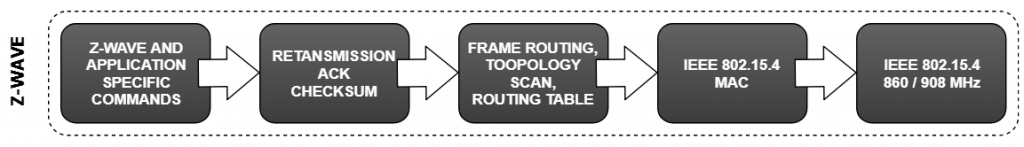
Z-Wave Protocol Stack
Advantages
- Easy to install the system
- Easy to add or remove devices
- Interoperable with other devices
- Comparatively cheap
- AES-128 bit encryption
Disadvantages
- Cannot be deployed over a wide area as the range is less.
- Only 232 nodes can connect to a hub.
- Apt for less data speed and small data size applications.
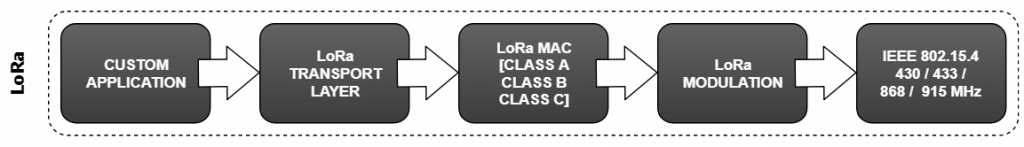
 LoRa
LoRa
LoRa is a proprietary, wireless communication technology. Cycleo of Grenoble, France, developed LoRa and Semtech acquired it later. It uses low-energy, sub-gigahertz, unlicensed frequency bands like 169 MHz, 433 MHz, 868 MHz and 915 MHz. This makes long-distance communication, in the range of more than 10kms, possible for a battery-operated device.
LoRa technology is built in two parts:
- LoRa physical layer: The LoRa physical layer protocol is proprietary and closed. Therefore, there is no freely available official documentation. However, several people have analyzed it and documented their findings. LoRa physical layer protocol enables the long-range communication link.
- LoRaWAN: LoRaWAN defines the communication protocol and system architecture for the network in the medium access control (MAC) layer protocol. It manages the communication between Low-Power Wide-Area Network gateways and end-node devices. LoRaWAN manages the communication frequencies, data rate, and power for all devices.
LoRa Protocol Stack
Platforms based on LoRaWAN
- Globalsat: both a public LoRaWAN and private LoRa Nodes solution (WW, include Europe, United States, Asia regions and Japan).
- ThingsConnected: a free platform provided by the UK Digital Catapult
- The Things Network: The Things Network is building a globally distributed, crowd-sourced and open IoT data network, owned and operated by its users. Using low power, long range technologies. The Things Network provides an end-to-end stack. From nodes to gateways, network server, device management and integrations with major cloud providers and IoT platforms. All are fully secure and configurable by the end user.
- iFrogLab: public LoRaWAN and LoRa (North America and Taiwan).
- IoT-X: a platform from Stream Technologies for public and private networks.
- ResIOT.io: a platform for private, public networks and IoT projects.
- OpenChirp: open management layer on top of LoRaWAN for data context, storage, visual representation, and access control.
- The Things Network: a free and open-source LoRaWAN network provider developed and supported by a worldwide community.
- Everynet: provides a platform and gateways for Lora (America, Europe and China).
- Actility: offers ThingPark Wireless, a network management platform for public LoRaWAN deployments and ThingPark Enterprise, for dedicated and private networks.
- Senet: public LoRaWAN provider (North America).
- LORIOT.io: global public LoRaWAN operator and platform for private and public networks.
- The LPWAN ecosystem.
Source for the platforms based on LoRaWAN is Wikipedia.
 Thread
Thread
The “Thread Group” alliance developed Thread. The “Thread Group” alliance, announced in 2014, has over 50 companies, including major players such as Samsung, Arm Holdings, Nest Labs, NXP etc.. It is an open, royalty-free, IPv6 based, secure technology, targeting low-power IoT products. All the features are oriented for its application in home automation. It uses It uses 6LoWPAN in the data link layer, which in turn, uses IEEE 802.15.4 in the physical layer. The main competitor for Thread is technologies like ZigBee and Z-wave.
Thread uses IPv6 for the Internet Protocol addressing and each of the devices is IP-addressable. The technology uses secure AES encryption to encrypt the transmitted data.
Thread Protocol Stack
Advantages
- Thread guarantees to be a “no single point of failure system”.
- Use of strong AES-128 encryption.
- Uses good security features such as proper authentication in order to join a network.
- IP-addressable devices.
- Uses 6LoWPAN, which acts as a bridge between the IEEE 802.15.4 devices and IPv6. This bridges two important technology.
- Backward compatibility across all versions.
Comparison
Conclusion
We have a lot of technologies in the market to choose from. How do we choose one?
Well, for a developer, it depends on the application. As a developer, one has to go through these technologies in and out to decide if it fits the mandate. Some product might have battery optimization as its core highlight. Some others have high data-rate as its selling point. It all depends on the use case of the product.
As a customer, most of the technologies promise the same thing, like ZigBee and Z-Wave. So the next thing that is logical is the cost, market availability and support from the company. Buying a high priced product with zero company support will prove to be useless. The next important thing to keep in mind is the compatibility of the standards. Fortunately, many brands of smart-home networking hubs are already compatible with two or more of these standards.
Will there be a single standard for IoT? It takes time to get to a logical conclusion. For a product market to grow, it needs to have global standards. Thus, the developers might come to an agreement on standards, but only time will tell. On the positive note, the developers have a long list of protocols to choose from.